A hacker by common definition is considered a computer criminal, or a microcomputer user who trespasses to gain unauthorized access to proprietary computers. Hackers re-configure or reprogram a system to function in a way not intended by the original programmer or the owner of computer. The hacker may also program or alter the original configuration, so as to enable the system access to the additional features not primarily incorporated therein. A hacker is like a double edged sword because, although commonly taken in negative sense yet can, hackers can and have rendered valuable services to the computer industry.
Although hackers can break into a computer system, they can strengthen its security too. In fact, World Wide Web and Internet have emerged in consequence of the efforts by famous hackers. An impression is that a hacker is one who can challenge and break in strong computer system. Those who use hacking negatively are called ‘Black Hats’ while those who do it for a positive purpose, are called ‘White Hats’. In case there is ambiguity in the motives of hacking then the hackers are known as ‘Grey Hackers’. They are usually, computer enthusiasts, hobbyists, administrators, computer programmers and system designers. Hacking in mainstream usage implies cyber crimes like identity theft, credit card fraud, breach of computer security, malfunction or alteration in video games and software cracking.
1. Kevin Poulsen

Kevin Poulsen also known as Dark Dante was born in 1965 in Pasadena, California. Currently a news editor for Wired dot Com, he was formerly a famous Black Hat hacker. His best known hacking event is the take-over of telephone lines of Los Angeles radio station KIIS-FM, securing for himself the position of 102nd caller, winning the prize of a Porsche 944 S2. He went underground when FBI started searching him. He was featured in ‘Unsolved Mysteries’ by NBC and 1-800 telephone lines of the Programme mysteriously crashed soon after the commencement of the program. However Kevin Poulsen was finally arrested in April 1991. He pleaded guilty to seven frauds of mail, wire and computer, money laundering and impediment of justice. He also confessed of breaking into computers and getting FBI related information. He was sentenced to 51 months imprisonment with & 56,000 fine. It was the longest punishment for any cyber crime of that time.
2. Donncha O Cearbhail ( Denis Carrol)

Donncha O Cearbhail was born to John Carroll in Birr, Offlay, Ireland. He was educated at Trinity College, Dublin. He won an Olympic medal in the field of computer science in 2011, while he was attending St. Berndan’s Community School. He was arrested on March 6, 2012 on suspicion of causing leakage of January 17 call between FBI and UK Serious Organized Crime Agency. He had been linked to a series of computer hacking events involving the high profile hacking group, commonly known as LulzSec. The group has been on the back of high profile targets like Paypal, Sony and even the FBI. He was held in Terenure Garda Station, Dublin and then released without any charge.
3. Stephen Wozniak

Stephen Gary Wozniak, nicknamed ‘Woz’ was born on August 11, 1950. He was an American computer engineer and programmer who founded Apple Computer. In 1970 he worked along with Steve Jobs at Hewlett Packard. After leaving University of California, Berkley he designed the hardware, circuit board and operating system to develop the computer that earned him fame. Woz started hacking by making ‘Blue Boxes’; the device which could by pass telephone switching mechanism to make free long distance calls.
4. Kevin Mitnick

Kevin Mitnick was born in Los Angeles on August 6, 1963. He was a famous hacker, computer security consultant and an author. He received his early education at Monroe High School and attended Pierce College and USC. He started using his talent just an early age of twelve and by using social engineering, bypassed the punch card system used in the Los Angeles Bus lines. In 1979 he got unauthorized access to the computer system of Digital Equipment Corporation. In 1988 he was charged, convicted and sentenced for 12 months for breaking into DEC’s network and copying its software. He also hacked into Pacific Bell voice mail computers. Kevin Mitnick was arrested on February 15, 1995 with more than 100 cloned cell phone codes and various false identifications in his possession. He was the most wanted computed criminal in US at the time of his arrest. Kevin Mitnick hacked into Digital Equipment Corporation systems, Nokia, Motorola, Fujitsu Siemens and many other computer systems on account of ‘ Intellectual curiosity ‘ and maintained, ‘I am not a hacker. I’m a security professional’.
5. Robert T. Morris

Robert T. Morris born to Late Robert Morris is co-author of Unix best known for developing the first ever computer worm. The worm was known as the ‘Morris Worm’ on the internet ,in 1988, while he was a student at Cornell University. The worm caused a loss ranging from $200 to &53,000. The motive behind his hacking was ‘to demonstrate the inadequacies of current security measures on computer networks by exploiting the security defects that Morris had discovered’. In accordance with the Computer Fraud and Abuse act, he was sentenced in December, 1990 to three years’ probation, 400 hours of community service and $10,050 fine.
6. Eric Corley
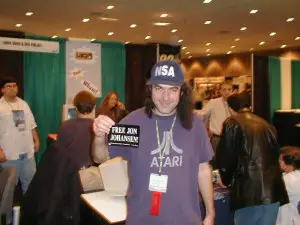
Eric Corley also known by his pen name; Emmanuel Goldstein, was born in Suffolk County, New York, US on December 16, 1959. He was educated at Stony Brook University and he is a popular writer, and Talk Show Host. His notable works include; 2600 Magazine, Dear Hacker, The best of 2600, and A Hacker Odyssey. Eric Corley is a prominent figure in the hacker community.
7. Jonathan James

Jonathan James also known as ‘c0mrade’ was born on December 12, 1983 and died on May 18, 2008 following self inflicted gunshot. His suicidal note read,’ I honestly, honestly had nothing to do with TJX. I have no faith in the justice system. Perhaps my actions today, and this letter, will send a stronger message to the public. Either way, I have lost control over this situation, and this is my only way to regain control’. James intruded high profile organizations like ‘Threat Reduction Agency Server’. He also cracked into NASA computers forcing NASA to shut its computers and bear a loss of about $1.7 million. James was sentenced to six months house arrest and probation until the age of eighteen.
8. Tim Berners- Lee

Sir Timothy John ‘Tim’ Berners Lee was born on June 8, 1955. He was an English computer scientist and is best known for inventing the World Wide Web. While studying at Oxford University he and one of his friends were caught hacking. He earned many awards. He was knighted in 2004, by Queen Elizabeth II for his pioneering work. He was also elected as a foreign associate of The United States National Academy of Sciences.
9. Adrian Lamo

Adrian Lamo was born to Mario Lamo- Jimenez and Mary Lamo Atwood in Boston, Massachusetts, US on February 20, 1981. He is a threat analyst and a ‘Grey Hat Hacker’. He attracted media attention after breaking into many high profile targets like The New York Times, Yahoo!, and Microsoft. Adrian Lamo was consequentially sentenced to six months detention at his parents’ home with two years probation and $65,000 fine.
10. Linus Torvalds

Linus Torvalds was born in Helsinki, Finland on December 28, 1969. He was a Finnish American hacker and software engineer. He is best known for the creation of open source Linux Kernel. He was honored with the 2012 Millennium Technology Prize ‘in recognition of his creation of a new open source operating system for computers leading to the widely used Linux Kernel’.
Conclusion:
The quest for self realization and the intuitive human urge to challenge, appears to be the primary motive for hacking. In 1903 Marconi boasted, ‘I can tune my instruments so that no other instrument that is not similarly tuned can tap my messages’. Moments before a scheduled demonstration, the Morse code message was disrupted into a meaningless rather insulting message. It had been hacked by the first famous hacker of all time; Nevil Maskelyne. He confessing to the Times, justified his actions on the ground of security holes, revealed for the public good. The ever increasing security holes and hackers coexist even after 100 years and seem to have brilliant future for many more similar years to come.










Leave a Reply